The 8-Minute Rule for Risk Management Enterprise
Table of ContentsThe Facts About Risk Management Enterprise UncoveredThe 9-Second Trick For Risk Management EnterpriseThe Facts About Risk Management Enterprise UncoveredThe smart Trick of Risk Management Enterprise That Nobody is DiscussingFascination About Risk Management Enterprise10 Easy Facts About Risk Management Enterprise ShownThe 8-Minute Rule for Risk Management Enterprise
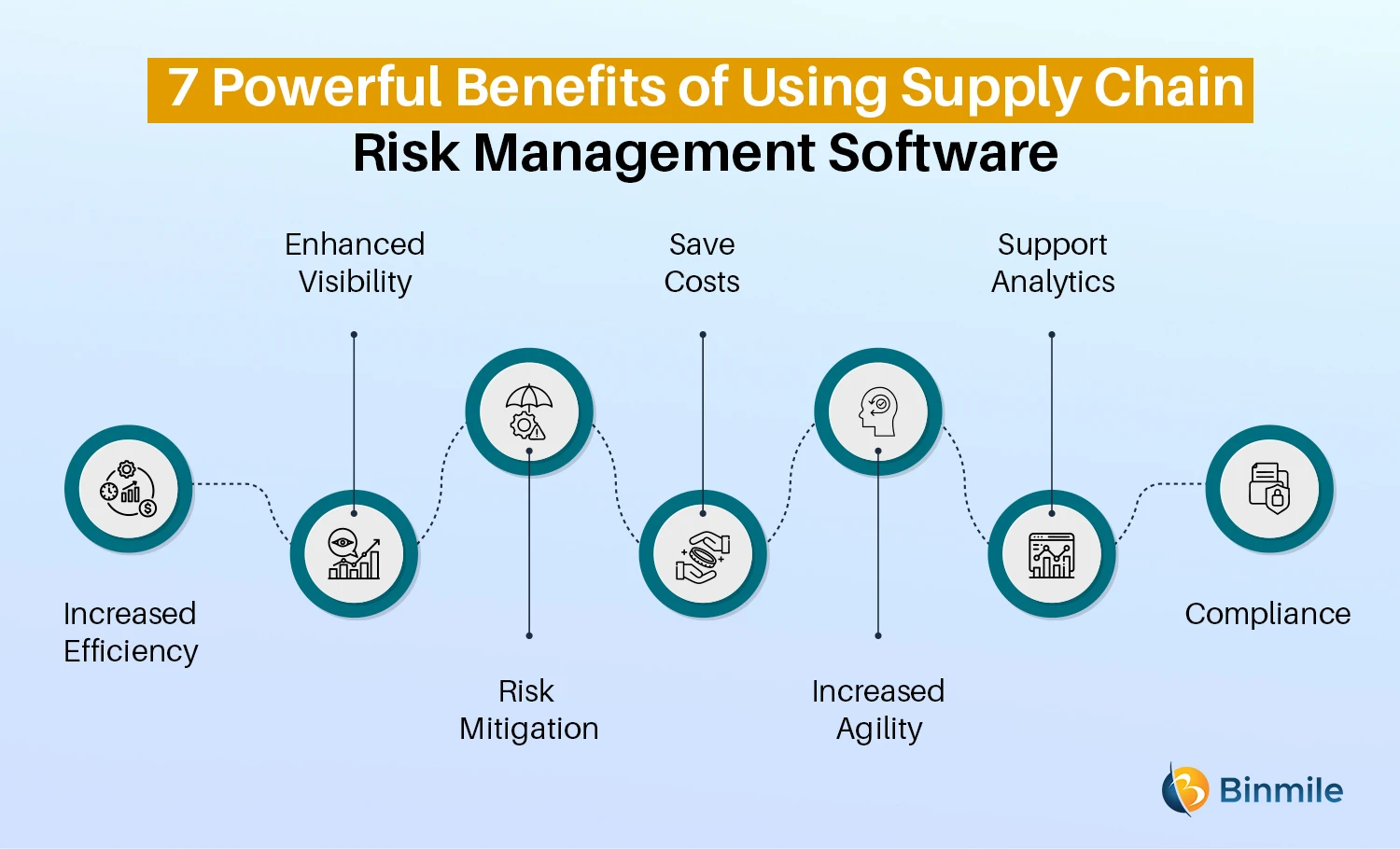
Right here are a few of its essential features that centers must recognize. Take a look. Real-Time Danger Analyses and Mitigation in this software program permit organizations to continually check and examine risks as they progress. This function leverages real-time information and automated evaluation to recognize prospective threats without delay. Once risks are recognized, the software application helps with immediate mitigation actions.
KRIs fix the issue of irregular or uncertain risk assessment. They attend to the difficulty of recurring danger monitoring by offering devices to keep track of threats constantly. KRIs improve safety risk oversight, making certain that possible risks are recognized and managed effectively. The job of threat monitoring ought to not be an obstacle. Companies have to rely on a first-class and innovative risk monitoring software program.
The smart Trick of Risk Management Enterprise That Nobody is Discussing
IT run the risk of monitoring is a part of business danger administration (ERM), developed to bring IT risk according to a company's risk hunger. IT risk management (ITRM) incorporates the plans, procedures and innovation necessary to decrease threats and vulnerabilities, while keeping compliance with applicable regulative requirements. On top of that, ITRM seeks to restrict the consequences of devastating occasions, such as security breaches.
Veronica Rose, ISACA board director and an information systems auditor at Metropol Corp. The ISACA Threat IT structure aligns well with the COBIT 2019 framework, Rose claimed.
Business Risk Management Software Application Development: Conveniences & Qualities, Price. With technical improvements, threats are continuously on the rise., companies browse with a regularly altering sea of risks.
Risk Management Enterprise Things To Know Before You Buy
In this blog site, we will study the world of ERM software, discovering what it is, its benefits, functions, etc to make sure that you can develop one for your service. Business Risk Monitoring (ERM) software application is the application program for planning, guiding, arranging, and controlling service tasks and streamlining risk monitoring processes.
With ERM, organizations can make insightful decisions to improve the total durability of the organization. Committed ERM systems are critical for services that regularly deal with substantial quantities of sensitive info and numerous stakeholders to authorize strategic decisions.
It can be avoided by making use of the ERM software program system. This system automates policy compliance administration to maintain the organization safe and certified.
Risk Management Enterprise for Dummies
You can likewise attach existing software application systems to the ERM using APIs or by adding data manually. Organizations can utilize ERM to examine threats based upon their possible influence for far better danger monitoring and mitigation.: Adding this attribute allows individuals to obtain real-time notifications on their gadgets about any kind of threat that might take place and its influence.
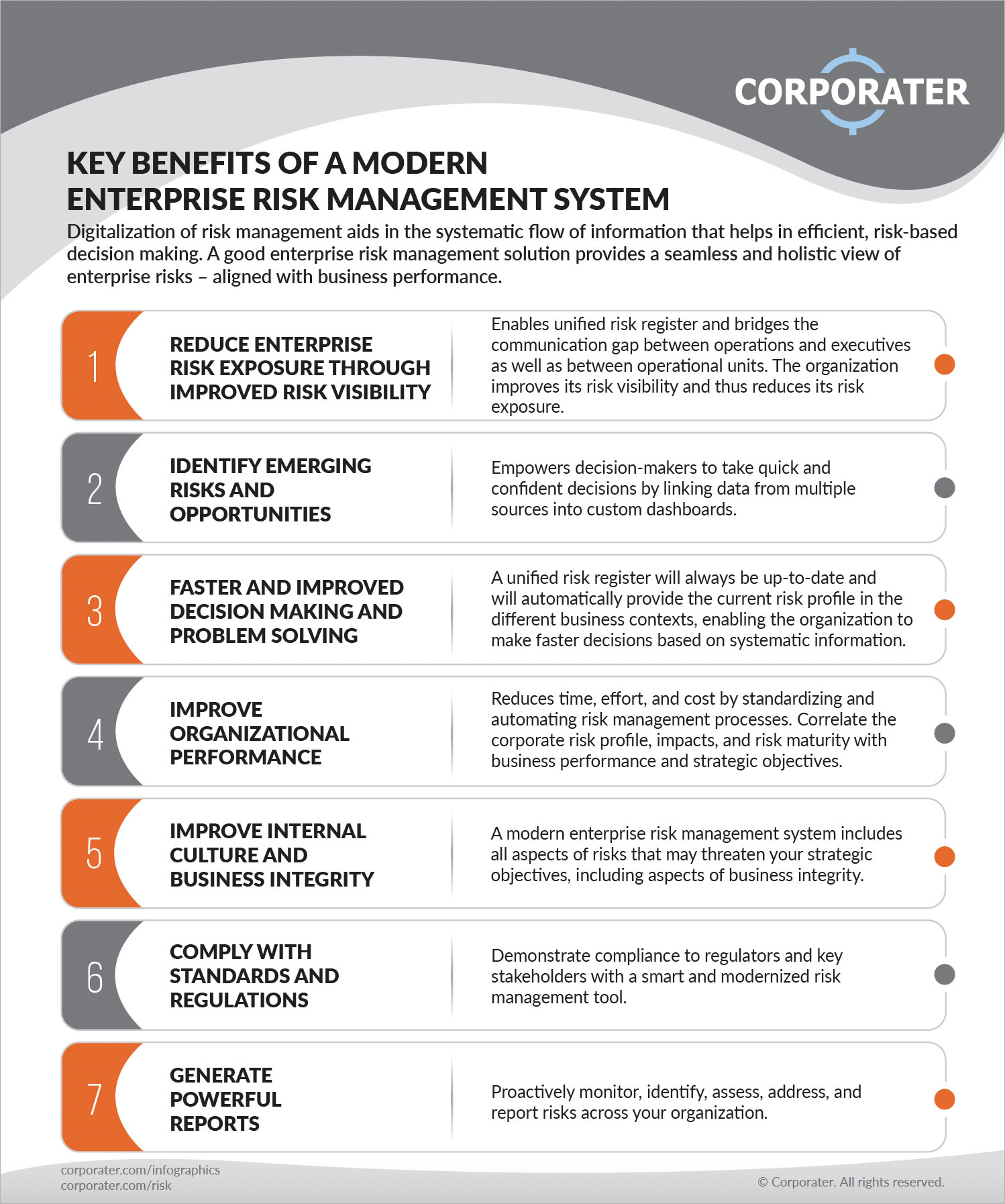
Rather, the software enables them to set thresholds for different processes and send push notices in situation of possible threats.: By integrating data visualization and reporting in the custom-made ERM software program, services can obtain clear insights about risk fads and performance.: It is required for organizations to follow market compliance and regulative criteria.

These systems make it possible for companies to apply best-practice risk monitoring procedures that straighten with industry requirements, providing a powerful, technology-driven approach to recognizing, evaluating, and mitigating threats. This blog site checks out the advantages of computerized risk administration devices, the areas of threat monitoring they can automate, and the worth they offer a company.
How Risk Management Enterprise can Save You Time, Stress, and Money.
Teams can set up types with the appropriate fields and easily produce various types for various risk types. These risk analysis types can be circulated for completion using automated process that send out notices to the pertinent staff to finish the types online. If kinds are not completed by the due date, then chaser emails are automatically sent by the system.
The control monitoring and control testing procedure can additionally be automated. Companies can utilize computerized workflows to send out routine control examination notices and personnel can get in the outcomes using on-line kinds. Controls can likewise be monitored by the software by setting regulations to send signals based on control information kept in other systems and spreadsheets that is drawn right into the system via API integrations.
Risk monitoring automation software application can likewise sustain with threat reporting for all levels of the business. Leaders can watch reports on risk exposure and control effectiveness with a variety of reporting outputs including fixed reports, Power BI interactive reports, bowtie evaluation, and Monte Carlo simulations. The ability to draw actual time records at the touch of a switch cuts out tough information adjustment jobs leaving risk groups with more time to analyze the information and suggest business on the very best course of action.
The demand for reliable has never ever been much more pressing. Risk Management Enterprise. Organizations operating in affordable, fast-changing markets can not afford hold-ups or inefficiencies in addressing possible risks. Conventional danger monitoring making use of hand-operated spreadsheet-based processes, while familiar, typically result in fragmented information, taxing reporting, and an increased likelihood of human error. Automating the danger monitoring process with software program addresses these drawbacks.
The Basic Principles Of Risk Management Enterprise
This makes sure threat signs up are always current and straightened with business objectives. Compliance is one more crucial chauffeur for automating threat administration. Requirements like ISO 31000, CPS 230 and COSO all offer advice around danger management finest practices and control structures, and automated threat click resources management tools are structured to straighten with these requirements aiding companies to satisfy most typically made use of danger monitoring standards.
Try to find threat software application systems with a permissions power structure to quickly establish process for threat acceleration. This functionality enables you to customize the view for each and every individual, so they just see the data pertinent to them. Make certain the ERM software program offers individual monitoring so you can see who entered what data and when.
Look for out tools that use project danger administration abilities to manage your jobs and profiles and the linked risks. The advantages of adopting threat administration automation software program prolong far past effectiveness.
Not known Incorrect Statements About Risk Management Enterprise
While the instance for automation is engaging, carrying out a danger monitoring system is not without its obstacles. For one, information top quality is important. Automated systems depend on accurate, up-to-date details to provide significant understandings. To get rid of the challenges of risk administration automation, organizations have to buy information cleansing and administration to make sure a solid foundation for executing an automated system.
Automation in risk management encourages companies to change their technique to take the chance of and develop a more powerful foundation for the future (Risk Management Enterprise). The question is no more whether to automate risk administration, it's exactly how soon you can start. To see the Riskonnect in activity,
The solution often depends on how well dangers are expected and managed. Job administration Web Site software application serves as the navigator in the troubled waters of job execution, offering devices that recognize and examine risks and create strategies to reduce them properly. From real-time information analytics to comprehensive threat monitoring dashboards, these tools give a 360-degree view of the project landscape, allowing project supervisors to make informed choices that keep their projects on track and within budget plan.